Modern DDoS threats require modern defenses
Secure your IP architecture and web applications.
Serverius offers 3 Tbps of always-on DDoS mitigation, with excellent tooling, control, and 24×7 support. The European DDoS scrubbing capacity will protect you when needed and reduce the threat of downtime.
We support you 24 hours a day
With proper pre-installation and configuration, users can count on professional assistance during DDoS attacks. Serverius’ escalation technicians are available 24/7 and keep your online business up and running.
By default, users can configure their own defenses upfront. During DDoS attacks, it offers you insights and functionality to change and improve all defenses. Non-urgent support questions will be answered within working hours and in case of an emergency, an “urgent request” will be answered within minutes.
The larger packages will offer users a personal DDoS assistant. This person will be your main contact for the technical service implementation, support, and urgent support requests, etc.

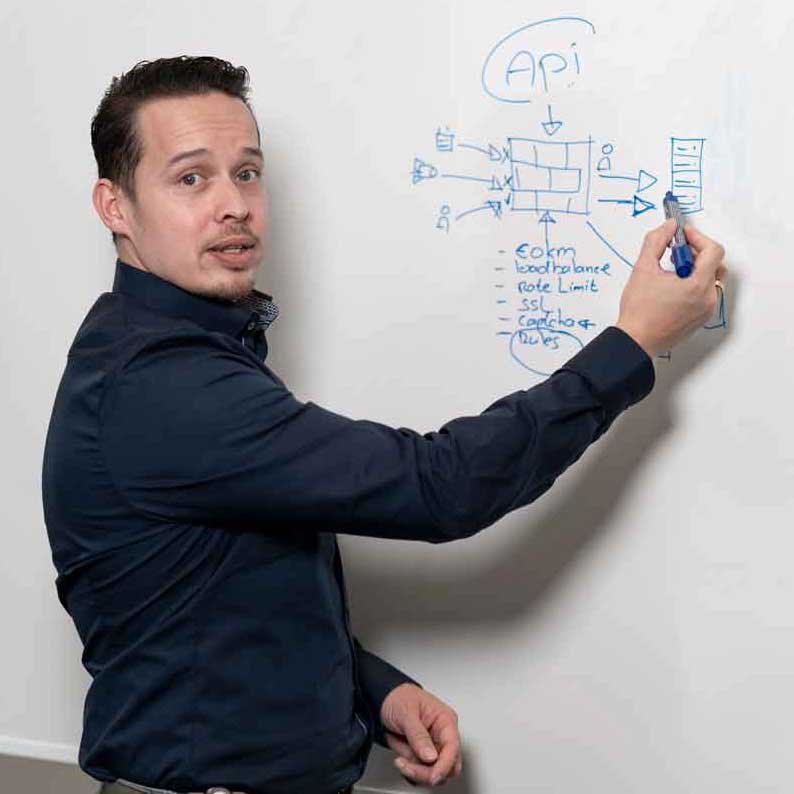
DDoS protection service training
Free DDoS protection service training for all clients.
Although all DDoS protection services are easy to use, you need to have the knowledge to use them in the best way possible. Because the success of every service defense is the way it’s integrated and being part of private infrastructure.
Every new user can use Serverius it’s free expert training. The engineer will explain the service its main features, he will perform a quick scan onto the protected IP subnets and applications, and he will explain how to handle during a DDoS attack. This way you don’t need to be a highly-skilled engineer yourself to manage your own environment. Everyone with basic IT knowledge can handle its default defenses, and when needed will be assisted by Serverius engineers.
This free one-to-one training (for paid service users) will normally take up to 2 hours. It can take place by telephone, chat, or at one of the Serverius office meeting rooms or private locations (travel cost will be invoiced as an extra).

DDoS IP Protection Service Level Agreement
Real-Time, automatic DDoS protection monitored and managed by Serverius experts.
When you want to outsource the monitoring, management, and proactive support of your protected domain, an additional SLA can be purchased. Serverius will take over
In addition to the default SLA, new responsibilities of both parties will be agreed upon by tailor-made SLA, which makes it clear in which cases Serverius engineers will act on behalf of you. Extra service guarantees will be added, additional infrastructure and application monitoring will be installed. Serverius will be 24×7 on your side.
Some parts of this tailor-made SLA are similar to the Serverius NOCaaS service. Therefore, our sales department can offer discounted pricing when both are purchased.